
LifeLock’s Use of un Vetted 3rd party Web Apps Compromised Millions of Users Personal Data
Identity theft protection firm LifeLock— a company that’s built a name for itself based on the promise of helping consumers protect their identities online — may have actually exposed customers to additional attacks from ID thieves and phishers. The company just fixed a vulnerability on its site that allowed anyone with a Web browser to index email addresses associated with millions of customer accounts, or to unsubscribe users from all communications from the company.
A flaw in the website design for LifeLock, a company charged with protecting the identity of its online customers, resulted in millions of customer accounts being exposed, according to KrebsonSecurity. A vulnerability in the site, which reportedly lacked authentication and security, has been fixed, but the breach highlights the larger security concerns inherent in web application security.
Of particular concern is the fact that web apps have become the cornerstone of operations for today’s digital enterprises. They are accessible at all times, from any location or device, but they can also contain sensitive customer data. Securing the data must be a priority, according to Setu Kulkarni, vice president of product and corporate strategy, WhiteHat Security.
“WhiteHat Security’s research has shown that web applications are consistently the most exploited means of entry into the enterprise by hackers. Despite this, companies are still failing to implement proper application security protections, making them an easy and vulnerable target.”
“We often see enterprises inheriting risk from third parties. In many cases, web pages are developed by non-IT teams without much governance. Data-flow architecture gets ignored, which can jeopardize personally identifiable information (PII). Largely by necessity, web applications are built and deployed by a wide range of coders, architects and administrators, who sometimes make mistakes.”
The vulnerability in a marketing page managed by one of LifeLock ‘s third parties serves as another reminder of the security issues in web application development, which often are not designed with security in mind. “Too many website applications are built with little thought on how to prevent being hacked,” said Chris Olson, CEO of The Media Trust.
“LifeLock’s web app vulnerability appears to have resulted from developers’ oversight and mirrors many other incidents in the past year alone, where security features and procedures to reinforce them receive little attention. Developers should make security a priority throughout a product’s life-cycle stages, from concept to manufacturing to retirement. Website operators should police all their website third parties to ensure all their activities fall within policies and scan their sites to identify and obstruct unauthorized code.”
The security incident echoes the reality that an unknown vulnerability can pose a major threat to data security and brand reputation, according to Rich Campagna, CMO, Bitglass. “Enterprises need to have visibility across their networks, cloud services and devices in order to prevent and monitor for these kinds of risks.
“This data leak could have been avoided by using data-centric security tools that can ensure appropriate configurations, deny unauthorized accesses and encrypt sensitive data at rest. Because LifeLock failed to utilize such a solution, millions of customers have had their data exposed, become more vulnerable to highly targeted spear phishing campaigns and lost trust in a company dedicated to keeping their data safe.”
The upshot of this weakness is that cyber criminals could harvest the data and use it in targeted phishing campaigns that spoof LifeLock’s brand. Of course, phishers could spam the entire world looking for LifeLock customers without the aid of this flaw, but nevertheless the design of the company’s site suggests that whoever put it together lacked a basic understanding of Web site authentication and security.
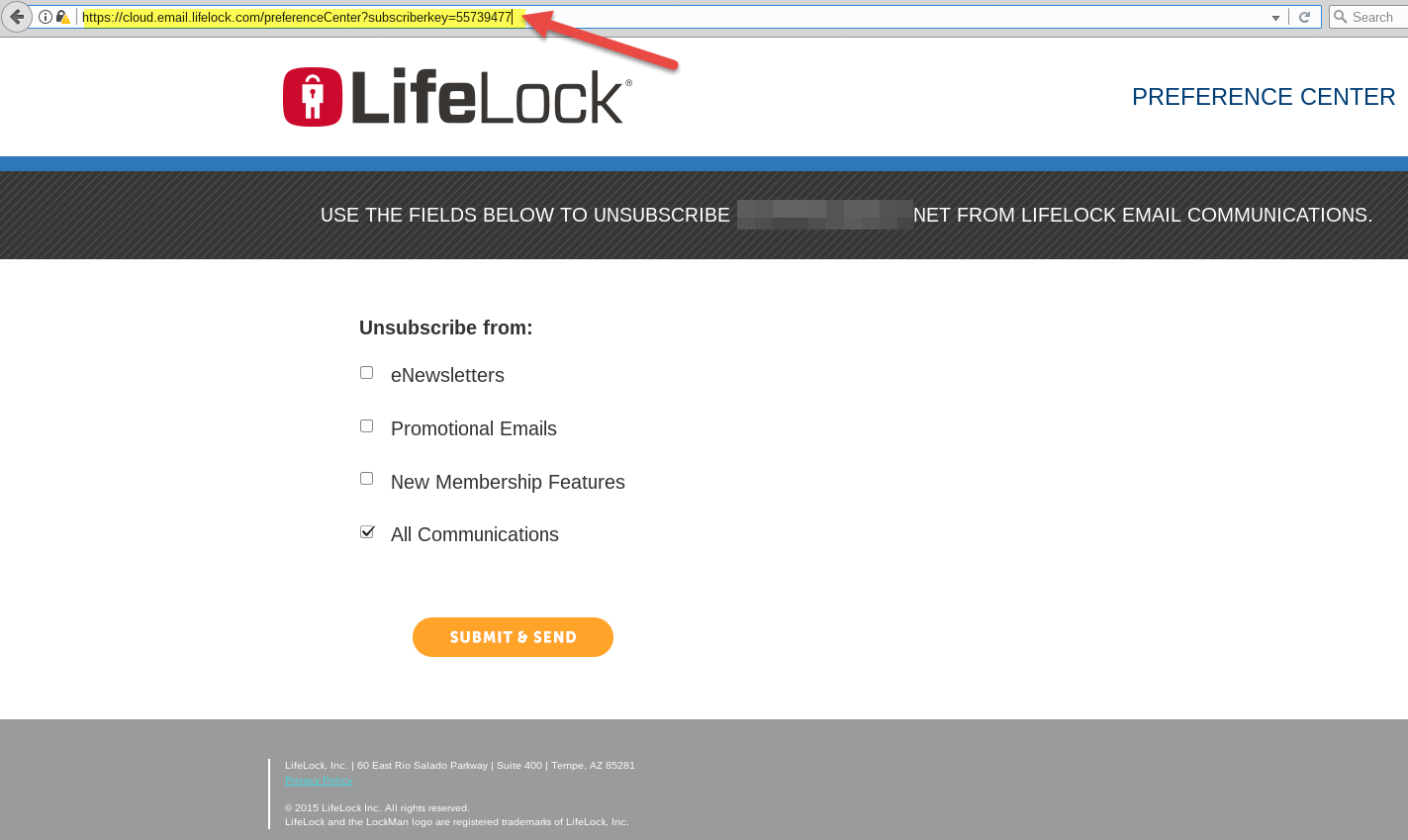
LifeLock’s Web site exposed customer email addresses by tying each customer account to a numeric “subscriberkey” that could be easily enumerated. Pictured above is customer number 55,739,477. Click to enlarge.
Pictured above is a redacted screen shot of one such record (click the image to enlarge). Notice how the format of the link in the browser address bar ends with the text “subscriberkey=” followed by a number. Each number corresponds to a customer record, and the records appear to be sequential. Translation: It would be trivial to write a simple script that pulls down the email address of every LifeLock subscriber.
Security firm Symantec, which acquired LifeLock in November 2016 for $2.3 billion, took LifeLock.com offline shortly after being contacted by KrebsOnSecurity. According to LifeLock’s marketing literature as of January 2017, the company has more than 4.5 million customer accounts.
KrebsOnSecurity was alerted to the glaring flaw by Nathan Reese, a 42-year-old freelance security researcher based in Atlanta who is also a former LifeLock subscriber. Reese said he discovered the data leak after receiving an email to the address he had previously used at LifeLock, and that the message offered him a discount for renewing his membership.
Clicking the “unsubscribe” link at the bottom of the email brought up a page showing his subscriber key. From there, Reese said, he wrote a proof-of-concept script that began sequencing numbers and pulling down email addresses. Reese said he stopped the script after it enumerated approximately 70 emails because he didn’t want to set off alarm bells at LifeLock.
“If I were a bad guy, I would definitely target your customers with a phishing attack because I know two things about them,” Reese said. “That they’re a LifeLock customer and that I have those customers’ email addresses. That’s a pretty sharp spear for my spear phishing right there. Plus, I definitely think the target market of LifeLock is someone who is easily spooked by the specter of cybercrime.”
LifeLock’s Web site is currently offline.
Misconfigurations like the one described above are some of the most common ways that companies leak customer data, but they’re also among the most preventable. Earlier this year, KrebsOnSecurity broke a story about a similar flaw at Panerabread.com, which exposed tens of millions of customer records — including names, email and physical addresses, birthdays and the last four digits of the customer’s credit card.
Content provided by Krebs On Security
Get discounts on LifeLock Membership
Update, 7:40 p.m.: Corrected the number of LifeLock subscribers based on a 2017 estimate by Symantec.
Update, July 26, 7:32 a.m.: Symantec issued the following statement in response to this article:
This issue was not a vulnerability in the LifeLock member portal. The issue has been fixed and was limited to potential exposure of email addresses on a marketing page, managed by a third party, intended to allow recipients to unsubscribe from marketing emails. Based on our investigation, aside from the 70 email address accesses reported by the researcher, we have no indication at this time of any further suspicious activity on the marketing opt-out page.